Active Threat - April 2, 2026
Running axios@1.8.4 or axios@0.30.0? You need to act now. Downgrade to axios@1.8.3 or axios@0.30.3, rotate every credential on affected machines, and block sfrclak.com and 142.11.206.73 at your firewall. Full steps below.
If you write JavaScript, you almost certainly use axios. It is the go-to HTTP library for everything from small React apps to large Node.js backends, pulling in over 100 million downloads every week. On the night of March 31, 2026, someone turned it into a weapon.
The group behind the attack is tracked as UNC1069, a financially motivated crew with ties to North Korea that has been active since 2018. They obtained a long-lived npm token belonging to the main axios maintainer, jasonsaayman, swapped the account email to a Proton Mail address they controlled, then quietly pushed two poisoned releases in a 39-minute window before anyone spotted what was happening.
What set this apart from a typical hijack was the preparation. The attackers staged everything 18 hours in advance, built separate payloads for Windows, macOS, and Linux, and made the malware delete itself after running. It wiped the dropper, swapped in a clean-looking package.json, and left almost no trace on disk.
100M+
Weekly downloads
affected package
1.1s
RAT deploy time
after npm install
39 min
Both branches hit
v0 and v1
6 min
First detection
Socket.dev
How It Unfolded: The Attack Timeline
Mar 30, 05:57 UTC
Decoy package published
A clean axios-mock package goes up on npm, establishing a paper trail to make the account look active and legitimate before the attack.
Mar 30, 23:59 UTC
Malicious payload staged
The real dropper is published, XOR-obfuscated with the key OrDeR_7077, ready to be pulled in as a dependency when the attack fires.
Mar 31, 00:21 UTC
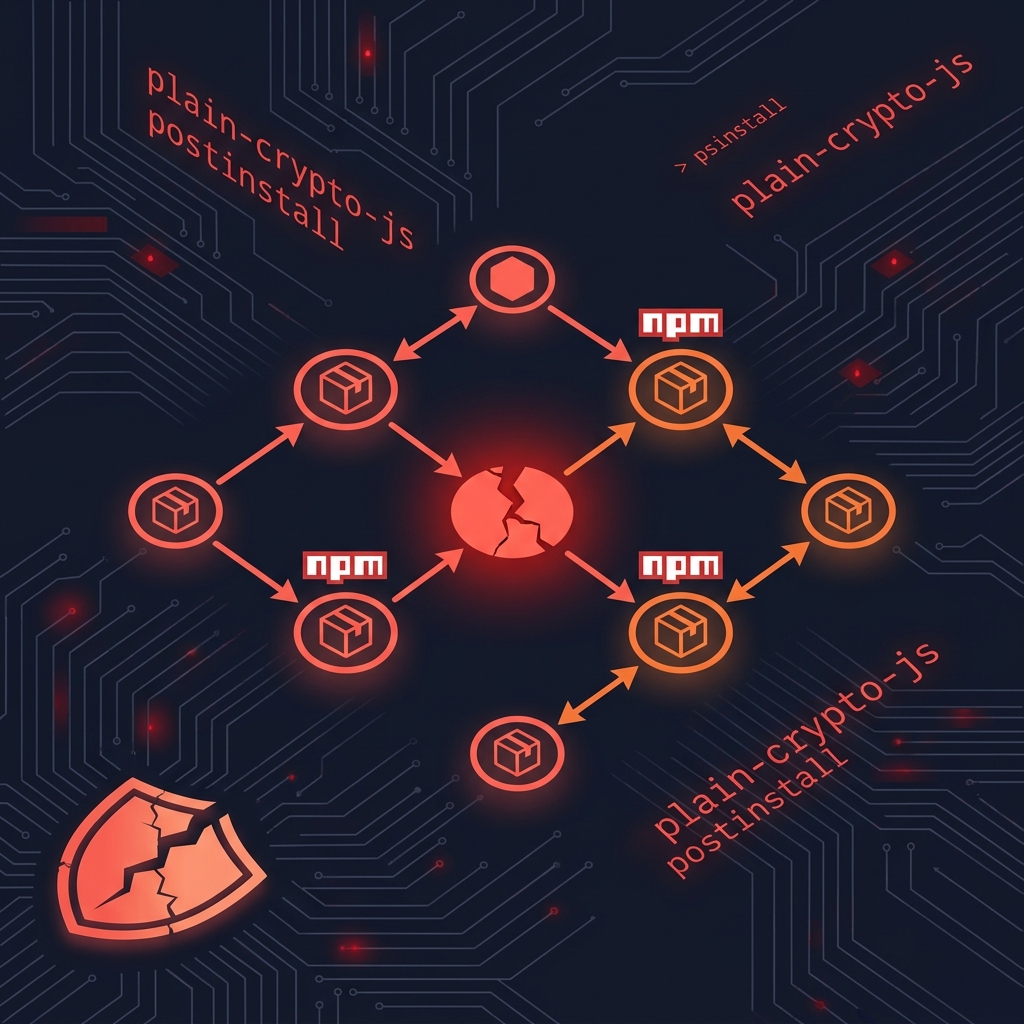
axios@1.8.4 released with backdoor
Using the stolen maintainer token, a new official axios release is pushed. One extra line slips into package.json: "plain-crypto-js": "^4.2.1". That package is never actually imported anywhere in the real axios code.
Mar 31, 01:00 UTC
axios@0.30.0 also compromised
Thirty-nine minutes later the legacy 0.x branch gets the same treatment, catching millions of projects that were still on older versions.
Mar 31, 00:27 UTC
Socket.dev flags it six minutes later
Automated behavioral analysis catches the phantom dependency. GitHub issues and community reports start rolling in quickly.
The Full Attack Chain
"This was not opportunistic. The malicious dependency was staged 18 hours in advance. Three separate payloads were pre-built for three operating systems. Both release branches were hit within 39 minutes. Every trace was designed to self-destruct."
Step-by-Step: How to Check if You Were Affected
The first thing to do is find out whether you were running one of the compromised versions and whether the dropper ever had a chance to run.
Compromised versions
axios@1.8.4axios@0.30.0Safe versions
axios@1.8.3axios@0.30.3# Check what version your project is using npm list axios # Check globally installed packages too npm list -g axios # Scan your whole machine for any axios installs (Mac/Linux) find / -path "*/node_modules/axios/package.json" 2>/dev/null | while read f; do version=$(grep '"version"' "$f" | head -1) echo "$f -> $version" done # The most important check: search lockfile history for the phantom dependency git log -p -- package-lock.json | grep "plain-crypto-js" # If this returns anything at all, keep reading carefully
Real axios has exactly three dependencies: follow-redirects, form-data, and proxy-from-env. If you see plain-crypto-js anywhere in your lockfile history, that is not ambiguous. That is tampering.
Stop before you delete anything. If the git command returned a result, do not just nuke the file and move on. The dropper ran the moment npm install executed. Even though it cleaned itself up, it had 1.1 seconds to phone home and drop a persistent RAT. Treat the machine as compromised and follow the steps below.
How to Fix It: Remediation Steps
- Block the C2 domains at your firewall first. Do this before anything else. Block
sfrclak.comand142.11.206.73:8000. As long as those are reachable, any already-infected machine is still under attacker control. - Downgrade axios right now. Run
npm install axios@1.8.3ornpm install axios@0.30.3for legacy projects. Commit the updated lockfile. - Get plain-crypto-js out of there. Remove it from
node_modulesand make sure it is gone from your lockfile. - Found RAT artifacts? Treat the machine as fully owned. Rotate everything: npm tokens, SSH keys, API keys, database passwords, cloud credentials. All of it.
- Check what got committed while it had access. Look for unexpected changes to pipeline configs, CI secrets, or any new tokens issued during the window.
RAT file locations to check:
- macOS:
/Library/Caches/com.apple.act.mond - Linux:
/tmp/ld.py - Windows:
%PROGRAMDATA%\wt.exe
Do not delete them yet. Preserve the files for forensics, disconnect the machine, pull every credential that was ever on it, and rebuild from a clean image.
How to Harden npm So This Cannot Happen Again
Pin exact versions in .npmrc
That ^ caret in "axios": "^1.8.0" is what let npm silently upgrade to the compromised build. Add save-exact=true to your .npmrc and you will always install exactly what you asked for.
Turn off postinstall scripts
The whole attack ran through a postinstall hook. One line stops it cold: ignore-scripts=true in your .npmrc. If a package needs scripts to work, you decide whether to trust it first.
Set a package age floor
npm config set min-release-age 3 tells npm to refuse any package published less than 3 days ago. The poisoned axios versions existed for hours, not days. That one setting would have blocked this attack entirely.
Consider pnpm or bun
Neither runs lifecycle scripts by default. This attack would not have worked at all on a pnpm or bun project. Worth considering for new projects.
# Drop these into your .npmrc and commit it save-exact=true ignore-scripts=true min-release-age=3 # In CI, always use npm ci instead of npm install npm ci # Installs exactly what is in the lockfile, no surprises # Add these defaults to your base Docker image too RUN echo "ignore-scripts=true" >> /root/.npmrc && \ echo "min-release-age=3" >> /root/.npmrc && \ echo "save-exact=true" >> /root/.npmrc
One command would have stopped this attack completely: npm config set min-release-age 3. The poisoned packages were live for hours, not days. A 3-day age floor would have prevented every machine from ever pulling them down. Run it now.
Indicators of Compromise (IOCs)
Use these to search your logs, firewall records, and endpoint detection tools for signs of infection.
| Type | Value |
|---|---|
| C2 Domain | sfrclak.com |
| C2 IP Address | 142.11.206.73 |
| C2 Port / Path | :8000/6202033 |
| XOR Obfuscation Key | OrDeR_7077 |
| Phantom Package | plain-crypto-js@4.x |
| macOS RAT Path | /Library/Caches/com.apple.act.mond |
| Linux RAT Path | /tmp/ld.py |
| Windows RAT Path | %PROGRAMDATA%\wt.exe |
| axios@1.8.4 SHA-1 | 2553649f2322049666871cea80a5d0d6adc700ca |
| axios@0.30.0 SHA-1 | d6f3f62fd3b9f5432f5782b62d8cfd5247d5ee71 |
What This Means for Your Business
This is not a vulnerability in the traditional sense where you patch a library and move on. The axios package itself was fine. The maintainer's account was the weak point, and through that single credential attackers reached every developer and CI system that ran npm install during a six-hour window. With 100 million downloads per week, the potential blast radius was enormous.
Huntress confirmed over 100 compromised hosts in the first 24 hours alone. Because the malware deletes itself, the real number is almost certainly higher. Google's Threat Intelligence Group attributes this to UNC1069, a North Korea-linked group that is primarily after money, which means stolen credentials and intellectual property are the most likely targets.
The forensic clock is ticking. Because the malware cleans up after itself, teams that did not catch this in real time may not be able to confirm or rule out compromise through a standard disk scan. If your engineers ran the affected versions and you have not started a forensic review, start one today.
Stolen credentials
WAVESHAPER.V2 gives attackers full remote access, script execution, and process injection. Any secret accessible to an infected process should be considered compromised.
It spreads through dependencies
Two other packages, @shadanai/openclaw and @qqbrowser/openclaw-qbot, were also distributing the same malware. Your transitive dependency tree is part of your attack surface.
Hard to detect after the fact
The self-destruct behavior makes it very difficult to know whether a machine was hit if you did not catch it live. Standard malware scans won't find what isn't there anymore.
Frequently Asked Questions
Is axios safe to use now?
Yes. The compromised versions have been removed from npm. As long as you are on axios@1.8.3 or axios@0.30.3, you are safe.
What is the WAVESHAPER.V2 RAT?
WAVESHAPER.V2 is a remote access trojan deployed by the attackers after the SILKBELL dropper runs. It supports full remote code execution, file access, OS command execution, process injection, and two-way encrypted communication with the C2 server at sfrclak.com. It was built separately for Windows, macOS, and Linux.
Would using npm ci have prevented this?
Not on its own, because npm ci still runs postinstall hooks. However, it installs from the lockfile exactly, so if your lockfile was committed before the poisoned versions were published, it would have protected you. The combination of npm ci plus ignore-scripts=true would have fully blocked the attack.
How did Socket.dev catch this in 6 minutes?
Socket.dev uses behavioral analysis on package publish events rather than waiting for CVE reports. It looks at what code a package actually does: does it make outbound network connections? Does it modify system files? Does it obfuscate itself? Those signals fired immediately when plain-crypto-js hit npm. This is why behavioral supply chain monitoring is more effective than CVE-based scanning for this class of attack.
"The real axios has only three dependencies. The addition of plain-crypto-js is unambiguous tampering. When npm processes this vendored axios, it installs plain-crypto-js and triggers the same malicious postinstall chain."
About Voiceyfy
We build secure, AI-powered voice agents for service businesses
Security is something we think about deeply, both in the software we ship and in what we recommend to the businesses we work with. Voiceyfy helps service businesses answer every call, book every appointment, and grow without adding headcount.
Sources
NetworkChuck · theNetworkChuck/axios-attack-guide on GitHub · Google Threat Intelligence Group (GTIG) · Socket.dev Security Research · Huntress Labs · StepSecurity · Unit 42 by Palo Alto Networks · The Hacker News · Cyber Security Agency of Singapore